Kubernetes Dashboard 设置用户密码登陆
2021年1月24日
仪表板是基于Web的Kubernetes用户界面。您可以使用仪表板将容器化应用程序部署到Kubernetes集群,对容器化应用程序进行故障排除,并管理集群本身及其伴随资源。您可以使用仪表板来概述群集上运行的应用程序,以及创建或修改单个Kubernetes资源(例如部署,作业,守护进程等)。例如,您可以使用部署向导扩展部署,启动滚动更新,重新启动Pod或部署新应用程序。
本次文档测试版本1.15,目前从v1.11-v1.20版本都可以进行使用,二进制安装参考我这个就可以,kubeadm请参考下面的配置

默认Kubernetes UI界面是使用token登陆,但是由于token相比较麻烦。我们这里使用密码登陆
适用于以下环境
- Kubernetes 二进制安装
- Kubeadm
Dashboard搭建
创建命名空间
[root@k8s-01 dashboard]# kubectl create ns kubernetes-dashboard
创建Dashboard rbac文件
[root@k8s-01 dashboard]# kubectl apply -f http://down.i4t.com/rbac-dashboard.yaml
clusterrolebinding.rbac.authorization.k8s.io/admin created
serviceaccount/admin created
创建dashboard
[root@k8s-01 dashboard]# kubectl apply -f http://down.i4t.com/dashboard-k8s.yaml
查看pod和svc
[root@k8s-01 dashboard]# kubectl get pod,svc -n kubernetes-dashboard
NAME READY STATUS RESTARTS AGE
pod/dashboard-metrics-scraper-78f5d9f487-xs9hj 1/1 Running 0 25s
pod/kubernetes-dashboard-54445cdd96-9qbxt 1/1 Running 0 25s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/dashboard-metrics-scraper ClusterIP 10.102.198.67 8000/TCP 25s
service/kubernetes-dashboard NodePort 10.110.102.186 443:30000/TCP 26s
查看secret
[root@k8s-01 dashboard]# kubectl -n kube-system get secret|grep admin-token
admin-token-ftpp5 kubernetes.io/service-account-token 3 16m
获取token
[root@k8s-01 dashboard]# kubectl -n kube-system get secret admin-token-ftpp5 -o jsonpath={.data.token}|base64 -d
eyJhbGciOiJSUzI1NiIsImtpZCI6Ikp4OS1oTzdRWW5ZOV9ianlma3ZhUkJfTndQclhQOWRrNEdSc19KM09NM00ifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJhZG1pbi10b2tlbi1mdHBwNSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJhZG1pbiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50LnVpZCI6ImMzYWVlMmQ1LTcwYzEtNGZiYi04ODE0LTc3MjllMmNhY2UwOSIsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXN5c3RlbTphZG1pbiJ9.XvNLLc8MXYcEW8yzW9aKyqUFEMf3vuvhbML4Fk_34RuD8980ZRRoqgEjW4usWEMvh7ftdxKo4fnz6tJjAfF0WgAF7E8VnS2Cyt_nC6irjQbd61rmdf42qPtSCrgwlhLfCjpse9N_iEvPhXp_1J-sN0aSi3lsjr4qSHhLzNZphwW6LvWO0EGVoubQyfEjKvIWaXTtqS1xxVkl-NcAqX1HIlUJqErLyAnwimQVqu-xb5K--mkCsHlMbyFV4lXtFDM5akctd92w-wnIh_uLoo1srzD-j8CvVmF0u2046mBI-d47-hVMrBy-eU_qi_gP5_TPafoJUy4u6icSjBzL5JzpgQ
访问测试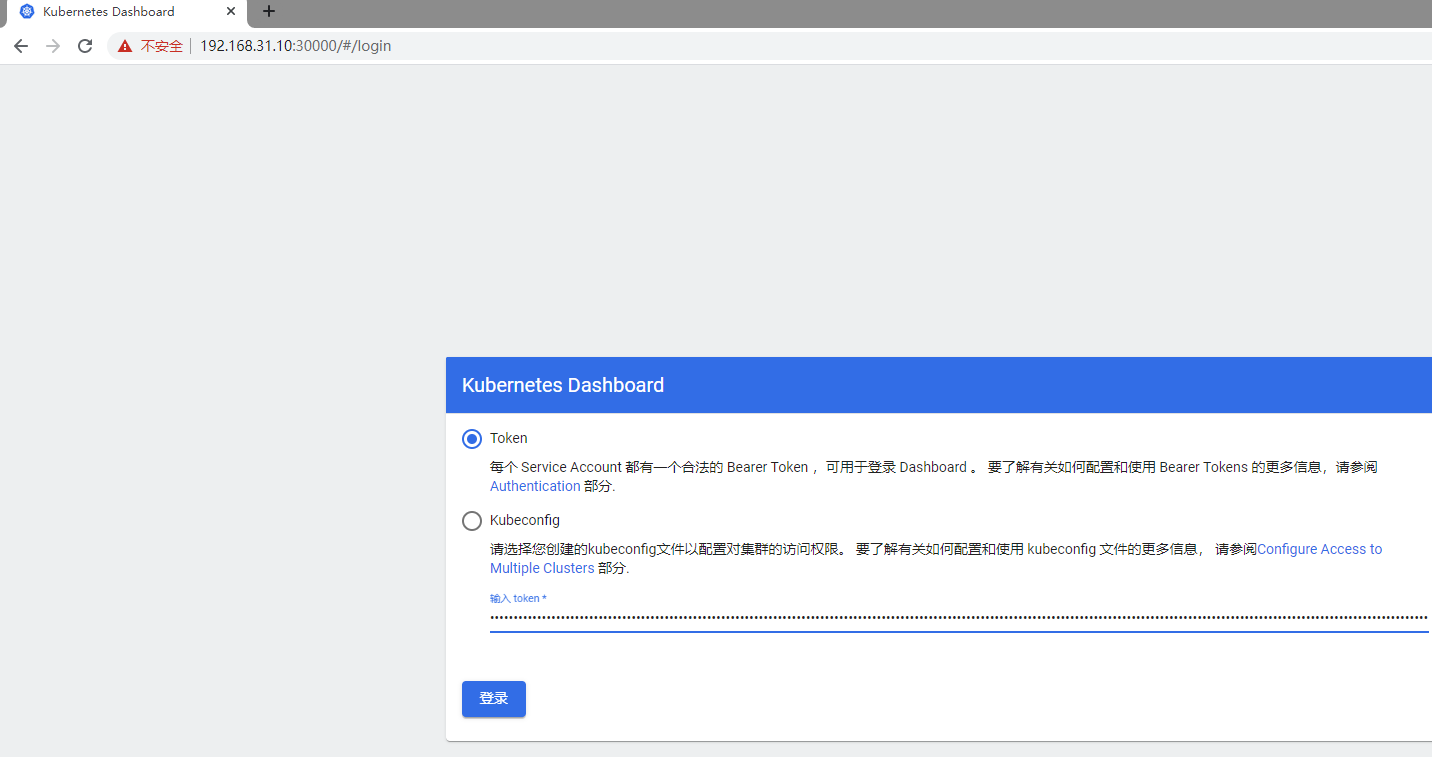

接下来进行修改账号密码登录
一、二进制Kubernetes搭建修改
1.首先确保K8S集群内部一切正常
[root@i4t ~]# kubectl get node
NAME STATUS ROLES AGE VERSION
yzsjhl82-138.opi.com Ready 22h v1.13.5
yzsjhl82-139.opi.com Ready 22h v1.13.5
yzsjhl82-140.opi.com Ready 22h v1.13.5
yzsjhl82-142.opi.com Ready 22h v1.13.5
[root@i4t ~]# kubectl get pod --all-namespaces
NAMESPACE NAME READY STATUS RESTARTS AGE
default busybox 1/1 Running 23 22h
kube-system coredns-d7964c8db-2t8wl 1/1 Running 1 22h
kube-system coredns-d7964c8db-sbztp 1/1 Running 1 22h
kube-system kube-flannel-ds-amd64-cv5hx 1/1 Running 2 22h
kube-system kube-flannel-ds-amd64-f2f7x 1/1 Running 2 22h
kube-system kube-flannel-ds-amd64-vmm74 1/1 Running 2 22h
kube-system kube-flannel-ds-amd64-zgfmq 1/1 Running 1 22h
2.配置
首先需要说明一点,默认kubernetes Dashboard是需要token登陆。不方便登记,我们可以让dashboard使用用户密码验证登陆

需要注意几点
- 修改apiserver
- 创建用户密码文件
- 创建yaml文件
[一] 在master上节点上创建文件(用户密码文件)
cat /etc/kubernetes/basic_auth_file
admin,admin,1
cyh,cyh,2
#前面为用户,后面为密码,数字为用户ID不可重复,经过测试账号密码要相同
[二] 在所有master的apiserver启动文件添加一行配置
vim /etc/systemd/system/kube-apiserver.service
--basic-auth-file=/etc/kubernetes/basic_auth_file
#启动路径可能不一样,请安装实际情况进行修改
#添加完毕后重启api-server
这里需要说明,以上操作在所有master上执行,在所有节点操作是为了防止有pod飘到非master节点,当然也可以做pod亲和力
[三]创建yaml文件
wget http://down.i4t.com/k8s-passwd-dashboard.yaml| kubectl apply -f k8s-passwd-dashboard.yaml
#创建绑定,将用户和权限绑定
kubectl create clusterrolebinding login-on-dashboard-with-cluster-admin --clusterrole=cluster-admin --user=admin
为了防止地址失效,我这里在手动cp一份
# ------------------- Dashboard Secret ------------------- #
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard2-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard2-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard2-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1beta2
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.8.3
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
- --authentication-mode=basic
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
type: NodePort
ports:
- port: 80
targetPort: 8443
nodePort: 30000
selector:
k8s-app: kubernetes-dashboard
我们可以用过下面命令进行检查kubectl get pod,svc -n kube-system
这里要说一点,我这里的镜像使用的是v1.8.3如果觉得版本低可以更高版本的。
访问dashboard界面
由于没有ingress,使用的是IP访问。所以会提示我们证书不安全,我们这里点击忽略直接访问。个别浏览器会造成打不开的,建议使用火狐
访问地址:https://master-IP:30000
在任意一台master上访问即可

这里需要我们输入api-server指定的文件里面的账号密码
跳过是没有权限查看k8s里面所有的信息


二、Kubeadm 环境配置
在所有的master节点配置用户名密码
echo "admin,admin,1" > /etc/kubernetes/pki/basic_auth_file
修改所有apiserver
vim /etc/kubernetes/manifests/kube-apiserver.yaml
#添加下面参数 (spec.containers.command下添加)
- --basic-auth-file=/etc/kubernetes/pki/basic_auth_file
#注意格式
修改完毕后api server会自动重启,等待重启成功我们访问dashboard即可
[root@k8s-01 dashboard]# kubectl get pod -n kube-system |grep apiserver
kube-apiserver-k8s-01 1/1 Running 0 24s
kube-apiserver-k8s-02 1/1 Running 0 44s
kube-apiserver-k8s-03 1/1 Running 0 50s
apiserver重启完毕后,添加dashboard Deployment配置
args:
- --auto-generate-certificates
- --namespace=kubernetes-dashboard
- --token-ttl=21600 #新增行 单位秒
- --authentication-mode=basic #新增行
也可以使用我提供的yaml,直接创建
kubectl apply -f http://down.i4t.com/dashboard-login.yaml
创建集群admin角色绑定 (否则无法登陆Dashboard)
kubectl create clusterrolebinding login-on-dashboard-with-cluster-admin --clusterrole=cluster-admin --user=admin
查看绑定
[root@k8s-01 dashboard]# kubectl get clusterrolebinding login-on-dashboard-with-cluster-admin
NAME ROLE AGE
login-on-dashboard-with-cluster-admin ClusterRole/cluster-admin 2m23s
创建
[root@k8s-01 dashboard]# kubectl apply -f k8s-dashboard.yaml
namespace/kubernetes-dashboard unchanged
serviceaccount/kubernetes-dashboard unchanged
service/kubernetes-dashboard unchanged
secret/kubernetes-dashboard-certs unchanged
secret/kubernetes-dashboard-csrf configured
Warning: kubectl apply should be used on resource created by either kubectl create --save-config or kubectl apply
secret/kubernetes-dashboard-key-holder configured
configmap/kubernetes-dashboard-settings unchanged
role.rbac.authorization.k8s.io/kubernetes-dashboard unchanged
clusterrole.rbac.authorization.k8s.io/kubernetes-dashboard unchanged
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard unchanged
clusterrolebinding.rbac.authorization.k8s.io/kubernetes-dashboard unchanged
deployment.apps/kubernetes-dashboard configured
service/dashboard-metrics-scraper unchanged
deployment.apps/dashboard-metrics-scraper unchanged





博主麻烦可以出一个权限的,我看报错是这个用户没权限,该如何配置,跪求 ✗笑哭了✗
下午我更新一下吧,这个就是rbac没有绑定好权限。 把dashboard的serviceaccount绑定到clusterrole的clust-admin就行
博主这个权限绑定咋弄的,有写文档不…
vim /etc/systemd/system/kube-apiserver.service
–basic-auth-file=/etc/kubernetes/basic_auth_file
看日志找不到文件,发现需要挂载到容器内部 ✗笑哭了✗ ,感谢博主
volumeMounts:
– mountPath: /etc/kubernetes/basic_auth_file
name: basic-auth-file
readOnly: true
volumes:
– hostPath:
path: /etc/kubernetes/basic_auth_file
name: basic-auth-file
大佬,/etc/kubernetes/basic_auth_file 这个文件我发现,账号和密码得相同才能登录,否则验证失败; 这个你有遇到过吗
目前没有,等我明天试一下给你答复。 我预计升级一下dashboard,改点东西进去。 建议吧可以使用开源的dashboard来管理集群,方便稳定
这个我刚刚试了下/etc/kubernetes/manifests/kube-apiserver.yaml里面的- –authorization-mode=None,RBAC要把None去掉改成- –authorization-mode=RBAC ,然后/etc/kubernetes/pki/basic_auth_file里面的格式是 密码:登录名:userid 第一个是密码,第二个是用户名,能正常登录。
[…] Kubernetes Dashboard 设置用户密码登陆 […]
大佬,按照这个教程https://k.i4t.com/kubernetes_dashboard.html搭建的dashboard,点击概况、工作负载等部分模块会提示未知错误404 the server could not find the requested resource这个需要怎么搞呀?是不是缺少service组件?
看一下是不是缺少metrics
对,没有这个,这个得咋搞
密码账号可以不一样,“should be password, user-name, user-id”
可以看这篇:https://stackoverflow.com/questions/35942193/kubernetes-simple-authentication